Stay with me on a thought experiment for a second, and assume the LLM inference cost is zero. What would that mean for security engineering?
Look at the diagram below.
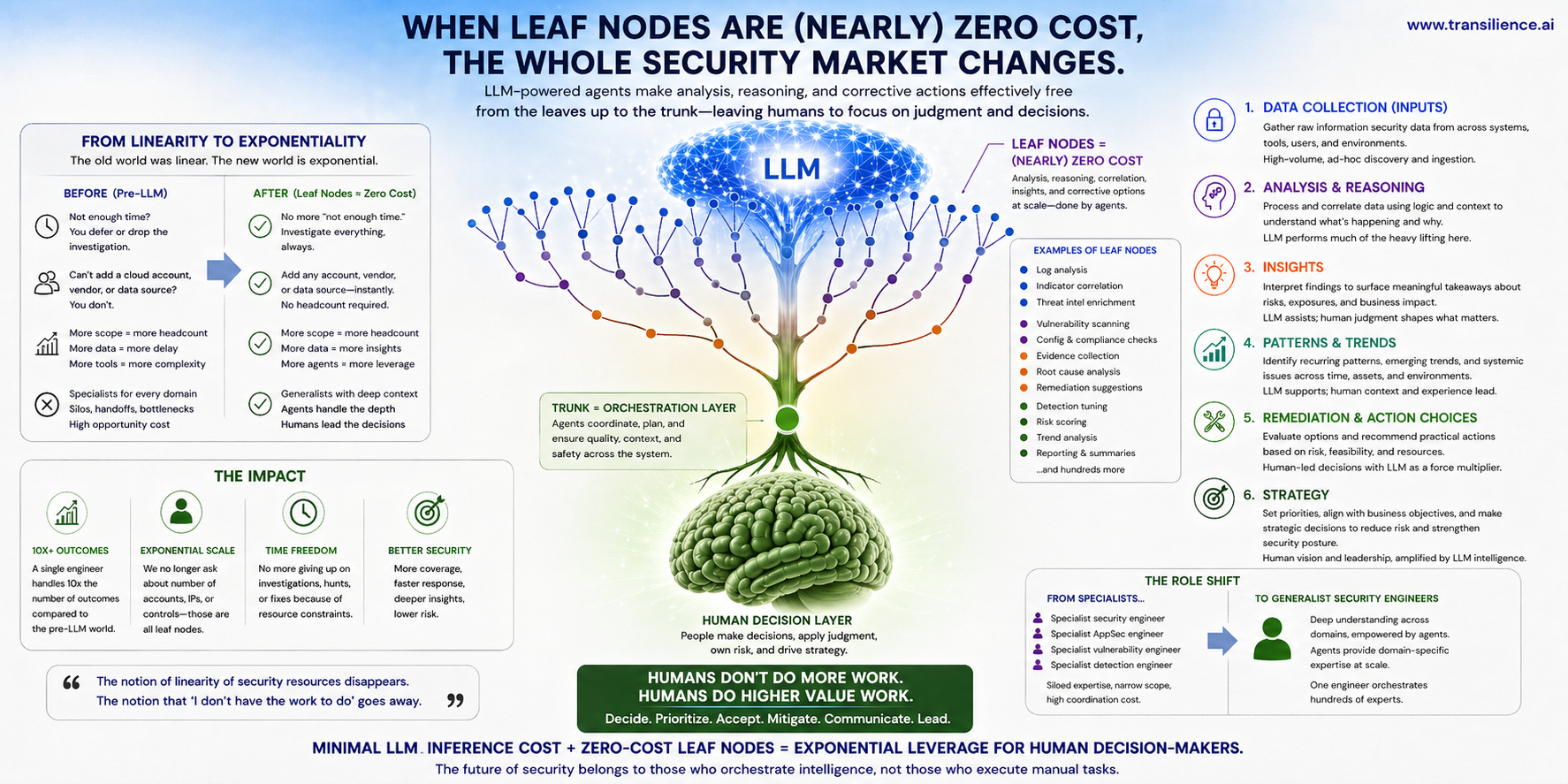
The LLM is doing the data collection. It's doing the analysis. It's doing the reasoning. It's offering insights. It's picking up on patterns and trends. All of it. And if inference is free, there's no ceiling on how often you run it. Run it a thousand times. Run it across every account, every endpoint, every log source, every control. The ceiling moves.
So what becomes possible?
The end of "we didn't have time"
Think about how many times you've walked away from a security task because the clock ran out. A threat hunt you scoped down. An investigation you closed as inconclusive. A vulnerability you triaged as "accept the risk" because nobody had the bandwidth to actually fix it. Think about the conversations that started with "let's not add another cloud provider" or "let's not onboard that vendor," not because it was the wrong call for the business, but because every new resource meant more work for a team that was already underwater.
That math changes. The linearity between security resources and security outcomes (more accounts means more analysts, more endpoints means more detection engineers) quits being a law of nature. The grunt work of investigation and research stops being the bottleneck. What's left for humans is the part that was always the hardest and most valuable anyway: decision-making. Judgment calls. Sitting with the analysis and recommendations the LLMs surface and deciding what to actually do about them.
Who's left in the room?
Here's where it gets uncomfortable for a lot of us. If the leaf node work is handled, do you still need a deep specialist for every domain? Today, a mature security org looks like a constellation of specialists. A specialist security engineer. A specialist application security engineer. A specialist vulnerability management engineer. A specialist detection engineer. Each one years deep in their corner. Each one a hiring problem.
Or do you instead need a generalist? Someone with enough fluency across each domain to understand and weigh risk, while letting the agents handle the domain-specific depth.
I think it's the generalist. And I don't think it's a prediction. I think it's already happening.
What we're seeing in practice
The number of security engineers needed to do security work has dropped exponentially in our experience. The questions we used to ask customers during onboarding tell the story.
We don't ask how many AWS accounts they have before we scope detection engineering anymore. We don't ask how many IP addresses are in scope before a pentest. We don't ask how many compliance controls need to be mapped against their configuration and evidence. All of that is leaf node work now. The count doesn't drive the staffing.
A single engineer today produces something on the order of 10x the outcomes that the same engineer would have produced in the pre-LLM world. That's not a productivity bump. It's a different shape of work.
The interesting question isn't whether this is coming. It's whether your org is structured for it.



